The Threat Has Shifted: Integrity as the New Attack Surface
A $25 million deepfake scam was not a glitch. It was a warning. As AI generated voices and video become nearly indistinguishable from reality, government faces a new battlefield where trust itself is the target.

.avif)
The Threat Has Shifted: Integrity as the New Attack Surface
No firewall failed. No endpoint alert triggered. No network perimeter was breached.
The incident underscored a new reality for government leaders: adversaries no longer need to penetrate infrastructure to disrupt operations. They can manipulate authenticity instead. Synthetic audio, video, and text can now be produced at scale, convincing enough to bypass human trust and fast enough to outpace traditional validation processes.
When personnel cannot reliably verify who is speaking or whether a directive is legitimate, the mission is placed at risk:
• Financial authorizations and operational directives can be fraudulently initiated.
• Decision cycles slow as organizations work to confirm whether communications are authentic.
• Adversaries exploit hesitation and uncertainty to gain time and advantage.
In this environment, the attack surface extends beyond networks and systems. It now includes information integrity, the "I" in the cybersecurity confidentiality, integrity, and availability triad, which protects the accuracy and trustworthiness of information.
How adversaries exploit the integrity gap
AI has dramatically lowered the cost of producing and distributing fake content. Adversaries can now pair synthetic media with traditional tactics like compromised distribution channels, bot networks, and coordinated amplification to inject false narratives that can disrupt operations during time sensitive events.
A notable example came in 2022, when a deepfake video surfaced showing Ukrainian President Volodymyr Zelenskyy appearing to order troops to surrender. The clip was pushed through compromised websites and social channels in an attempt to confuse military personnel and slow response efforts, demonstrating how even imperfect fake media can create operational drag.
Adversaries’ goal is not always persuasion. Often, it is delay: slowing decision cycles, creating competing versions of events, or forcing government agencies to spend precious time proving their communications are real.
The risk also extends inside government networks. When provenance, the ability to verify a message’s origin and history, is not clearly established, AI enabled agentic tools that draft, summarize, or act on information can unintentionally amplify manipulated inputs.
Adversaries do not need to breach systems to gain advantage. They only need to undermine the integrity of the information those systems rely on.
What can we do about it?
With so much misinformation circulating, the biggest challenge is that government agencies lack a reliable, scalable way to prove what is real. Addressing that gap requires a shift from platform based trust, relying on where a message appears, to protocol based trust, verifying a message’s origin, lineage, and integrity regardless of where it travels.
Several actions are emerging as both practical and necessary:
- Make provenance a default feature of official content.
Government communications need tamper evident metadata that establishes when the content was created, who authorized it, and whether it has been altered. This is the foundation of content authenticity standards like C2PA and related content credentials. - Use blockchain or distributed ledgers to anchor authenticity.
Blockchain is not a silver bullet, but it offers a strong architecture for storing cryptographic signatures, timestamps, and change histories in a way that is decentralized and extremely difficult to falsify. When paired with provenance standards, it provides agencies with a verifiable record that can survive reposts, screenshots, and adversarial manipulation. - Require proof of human for consequential communications.
As AI generated media increases, agencies need a secure way to attest that a human decision maker approved the final message. Modern cryptographic approaches allow this without exposing personal data, preserving both accountability and privacy. - Hold agentic systems accountable.
Content drafted or summarized by AI assistants should automatically include a disclaimer that it was generated in part by AI. Provenance must reflect machine involvement, and policies should limit when and how automated systems can publish or act without explicit, verifiable human authorization. - Build time to confidence into crisis planning.
Crisis preparation exercises should not only measure how fast agencies can respond, but how fast the public and partner agencies and organizations can verify that the response is real.
For cyber teams accustomed to defending networks, these steps represent the parallel mission of defending trust in the information those networks carry. By shifting from trust by assumption to trust by verification, agencies make it far harder for adversaries to weaponize uncertainty.
The federal momentum already underway
Federal agencies are not starting from zero. Work is already underway across government to define how provenance, transparency, and multimedia integrity should function in practice.
NIST’s AI 100-4 guidance establishes technical foundations for provenance, watermarking, and labeling of synthetic content, while the AI Risk Management Framework now includes generative AI profiles that map model integrity and provenance controls directly to federal risk language.
On the operational side, NSA, FBI, and CISA have issued joint advisories treating deepfakes as a multimedia integrity threat, recommending adoption of Content Credentials and tamper evident workflows. CISA’s election integrity and Mis, Dis, and Mal Information efforts have also provided a framework for incident response, shifting from time to statement toward time to confidence.
The broader ecosystem is aligning as well. Standards bodies like C2PA and the Content Authenticity Initiative are creating open, interoperable specifications for content provenance and cryptographic signatures that can be adopted across federal systems.
Together, these efforts form the foundation for a government wide approach to verifiable authenticity that agencies can start implementing today.
Evolving from publishing to proving
For decades, government agencies have focused on distributing information quickly through official channels. In an environment saturated with inauthentic media, that is no longer enough. The public does not just need to hear from government; they need to verify government.
Leaders must establish a new norm where consequential communications like alerts and safety notices are cryptographically signed, provenance rich, and easy for stakeholders to confirm in seconds. Unsigned or unverifiable content can no longer be treated as authoritative.
The goal is not to eliminate misinformation. Today, that is impossible. Rather, it is to make authentic government communications provable in seconds, even when copied, reposted, or reframed by adversaries. When verification is fast, automated, and user friendly, government can better maintain public trust during crises and adversaries lose the ability to weaponize uncertainty as a default advantage.
.avif)
.avif)
RELATED POSTS

Moltbook The First Social Media Platform for AI Agents
What happens when AI agents interact without humans in the loop? Moltbook offers an early signal of what that could mean for trust, security, and autonomy as these systems scale.

Adapt Forward Selected for Missile Defense Agency’s SHIELD Contract to Support Nation’s Golden Dome Initiative
Adapt Forward, a veteran-owned cybersecurity firm supporting the Department of Defense (DOD) and other federal agencies, has been selected by the Missile Defense Agency (MDA) to compete for task orders under the Scalable Homeland Innovative Enterprise Layered Defense (SHIELD) contract.

Mike Small Returns to Adapt Forward
Micheal Small as attack sensing and warning (AS&W) technical lead. A retired Army veteran and accomplished cyber professional, Small brings more than two decades of experience leading offensive and defensive operations across military, intelligence, and commercial cyber domains.

Moltbook The First Social Media Platform for AI Agents
What happens when AI agents interact without humans in the loop? Moltbook offers an early signal of what that could mean for trust, security, and autonomy as these systems scale.

Adapt Forward Selected for Missile Defense Agency’s SHIELD Contract to Support Nation’s Golden Dome Initiative
Adapt Forward, a veteran-owned cybersecurity firm supporting the Department of Defense (DOD) and other federal agencies, has been selected by the Missile Defense Agency (MDA) to compete for task orders under the Scalable Homeland Innovative Enterprise Layered Defense (SHIELD) contract.

Mike Small Returns to Adapt Forward
Micheal Small as attack sensing and warning (AS&W) technical lead. A retired Army veteran and accomplished cyber professional, Small brings more than two decades of experience leading offensive and defensive operations across military, intelligence, and commercial cyber domains.
Lessons from the Nuclear Weapons Agency Breach
Lessons learned from the Toolshed Nuclear Weapons Agency Breach

AI in the Defense Sector: Balancing Innovation with Operational Risk
A thought piece that discusses upcoming challenges of AI in the Defense Sector
Employee Spotlight: Joe Fulco Wins NCMS Society Award – Again!
Employee Spotlight: Joe Fulco has once again been honored with the prestigious NCMS Society Award, recognizing his outstanding contributions to the field of National Industrial Security.
What is Model Context Protocol?
What is Model Context Protocol? What are the Benefits? What are the Risks?
An educational piece that educates on Model Context Protocol and what it means for the DoD
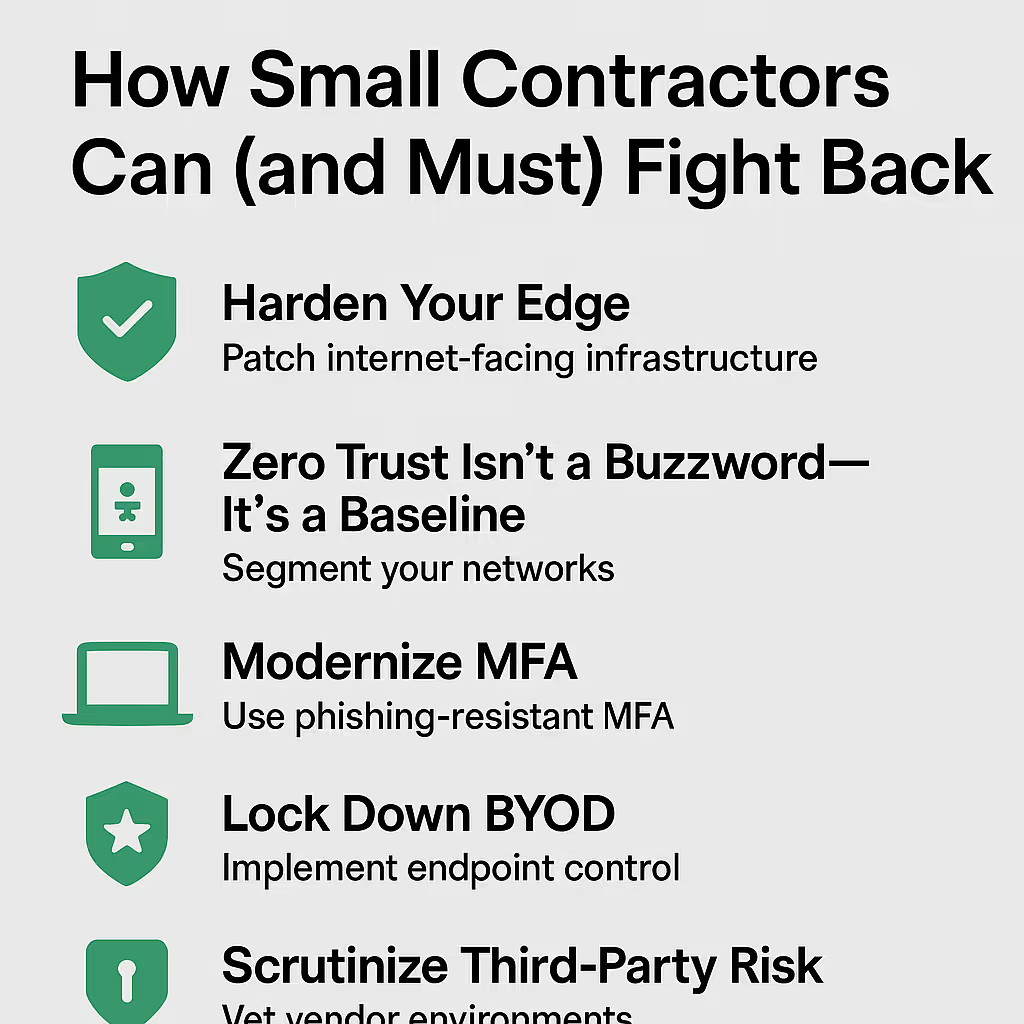
The 2025 DBIR Is Clear: Small Defense Contractors Are the New Primary Target
Verizon 2025 DBIR and what it means for Small Defense Contractors
In the world of cybersecurity, perception lags behind reality. Many small and mid-sized defense contractors still believe they fly under the radar. The 2025 Verizon Data Breach Investigations Report (DBIR) puts that myth to rest.
What Happens When CVE Goes Dark?
The Hidden Threat to DoD Cyber Strategy, Zero Trust, and AI Modernization
In this thought leadership piece, Adapt Forward addresses the urgent need to modernize our national vulnerability intelligence infrastructure. The near-shutdown of the CVE program exposed a systemic fragility in the foundation of Zero Trust, AI-driven defense platforms, and CTEM pipelines. While CVE has served as a critical baseline for decades, it’s no longer sufficient in a world where adversaries move at machine speed. This article breaks down why CVE can’t be sunset overnight—but must evolve into a risk-aware, threat-informed, AI-compatible system. We outline the future: predictive scoring, contextual enrichment, and mission-driven collaboration across public and private sectors.

Hire Vets Gold Award
Adapt Forward Earns 2024 HIRE Vets Gold Medallion Award – For the Second Year in a Row
We are proud to announce that Adapt Forward has once again been awarded the HIRE Vets Gold Medallion by the U.S. Department of Labor—marking our second consecutive year receiving this prestigious national honor.

James Cogswell Award
Adapt Forward Receives 2024 James S.Cogswell Award for Outstanding Industrial Security Achievement
We’re proud to announce that Adapt Forward has been selected as a 2024 recipient of the James S. Cogswell Outstanding Industrial Security Achievement Award by the Defense Counter Intelligence and Security Agency (DCSA).

Inc 5000
Adapt Forward Named to the 2020 Inc. 5000 List of America’s Fastest-Growing Companies
We’re thrilled to announce that Adapt Forward has been ranked #542 on the 2020 Inc. 5000 list, the most prestigious ranking of the nation’s fastest-growing private companies!









.avif)